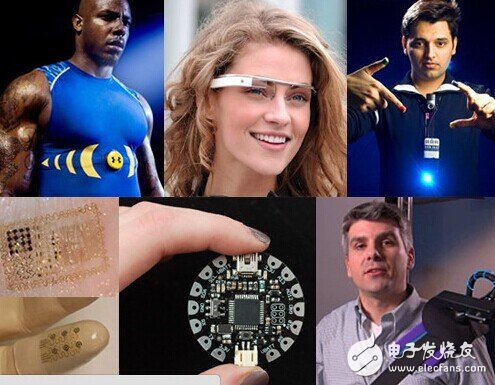
Smart wearable devices are the hottest technology force in the past two years, especially in the premise that both tablets and smart phones are in a weak situation, wearing equipment and smart cars, the Internet of Things and other next-generation technology. It is even more conspicuous.
However, in addition to the expanding market players, the wearable device industry has not been less questioned, but the main direction of questioning has changed from the original bubble or not to the concern about the safety risks of wearable devices. More and more people are beginning to realize that wearer devices, more dense and close-knit smart computing devices, will become the next source of data security.
At the recent 2015 HackPWN Safe Geek Carnival, a white hat hacker submitted a loophole on the Xiaomi bracelet to the organizing committee. Through the live demonstration, it can be seen that with this vulnerability, the hacker can take over the control of the Xiaomi bracelet, and after it cracked the reporter's Xiaomi bracelet, the latter suddenly kept vibrating, and the staff successfully read it on his mobile phone. The number of steps in the reporter's bracelet is exactly the same as that displayed on the reporter's mobile phone.
However, this is not the first accident in which a wearable device has been attacked by a hacker. As with the initial stage of the PC and the smartphone, there are still many security blind spots in the wearable device.
Why is the wearable device easily cracked?
The main reason for the wearable device is that it is cracked. The main factor is two aspects. First, the wearer's own shape determines that its security protection is not high. Currently, the wearable devices on the market are generally in a small form, and the function realization mainly depends on various sensors. Working, there is no chip or system layer, and it lacks protection in hardware and software.
On the other hand, the current design logic of wearable devices is to connect smart phones via Bluetooth, WiFi, etc., and then use GPS or mobile APP to synchronize data. In each of these joints, there is a possibility of data leakage and equipment being overcome. For example, the Xiaomi bracelet loophole mentioned above is that the hacker bypassed the reporter's mobile phone by using the loophole on the Bluetooth interface and directly took over the user's wearable device.
It is worth mentioning that although Apple and Google have long recognized the natural weakness of wearable device security, both Android Wear and Apple Watch are trying to avoid possible software security issues in the architecture, such as allowing third-party applications to It does not exist as a stand-alone application, but works as an adjunct to mobile applications. Even so, interfaces such as Bluetooth and WiFi are still a breakthrough for wearable devices.
Wearable device security crisis, data is not in hardware
After the wearable device was compromised, the most intuitive result was that the device was controlled and the data was stolen. These two points do not seem to be worth paying attention to at the moment. But in fact, in the context of the era of big data, its impact on users will be huge and far-reaching.
For example, when the device is controlled, then the hacker can control certain functions of the device, such as Alipay's Alipay-free payment, and unlocking the phone at close range, which may bring hidden dangers to user property security. In addition, wearable devices are increasingly moving toward the "key" role of managing cars, guest rooms and smart homes. Once hacked, the personal safety of users will also be threatened.
In the longer term, after the wearer and the smart medical care are more closely integrated, the wearable device will become the steward of personal health. At that time, the existence of these insecurities is not enough to completely deliver the safety of the user to others.
On the other hand, the device security of wearable products is by no means limited to the device itself, because almost all wearable devices are connected to mobile devices via Bluetooth or WiFi, which is to control the mobile phone by controlling the less encrypted wearable devices. Provided the possibility. For example, the Xiaomi bracelet, due to its diversified functions, will inevitably lead to more types and extents of access rights than general products. As a result, when there is a problem with its security, it will become a secret for users to leak mobile phone data. aisle.
The wide attention paid by many people in the scientific and technological circles also shows that the hidden dangers and the possible consequences of wearing equipment are not only worrying.
If you look down on the heavy wearable equipment, you should do your part.
In summary, it is not difficult to see that the wearer's body is not as petite as it is, but it is a very crucial "key" identity. These factors determine that the wearable device is burdened on its development path.
And the wearable equipment industry has always had a different line policy, that is, the problem of "light" and "heavy". Products that pay attention to "light" often show a focus on products that focus on "heavy". They want to provide some cross-border functions in addition to the basic functions - the former's representative such as Microsoft bracelet, OAXISO2 heart rate The bracelet, etc., the latter is represented by the millet bracelet.
In fact, these two development directions are not right or wrong in essence, especially considering that the wearable device is still unable to obtain large-scale user stickiness, the latter is still the trend. Because whether it is an Internet company that wears equipment or a purely intelligent hardware manufacturer, it is essentially a development of a service company, and big data is its core competitiveness. Only when sufficient users are allowed to use time and viscosity can they obtain sufficient and accurate data.
This is good in the original intention, but if we add the "safety" factor to comprehensive consideration, it is not difficult to see that this is also an irresponsible behavior for users, especially in the development of the wearable device itself. In the early days, still in the big environment where smartphones can't be separated, this model can't help but be too hasty, and companies should realize that they can't just look at the immediate interests, but neglect the protection of user data, regardless of long-term development -- to know, security issues Perhaps it is not a stumbling block for the development of wearable equipment, but it will definitely be an important indicator for the elimination of wearable products.
This may explain why the new OXIIS smart hardware products released in the middle of this year still focus on the motion monitoring function, and do not add some functions that seem to be intelligent but can not help but gimmick. This kind of concentration and persistence is actually an embodiment of the pursuit of the ultimate.
At present, the O2 heart rate bracelet launched by OXIIS and the fashion smart bracelet "Tiger Shadow" launched in cooperation with the fashion designer brand JiCheng have been launched on the Pozible, and they have a healthy and balanced life. This is actually the original intention of the development and popularization of new technology products such as wearable devices, and OXIIS has undoubtedly become the most professional and dedicated representative brand among them.
True Wireless Bluetooth Earbuds
Truly Wireless Earbuds,Best Truly Wireless Earbuds,Best True Wireless Earbuds Under,Best True Wireless Earbuds Under 50
Dongguang Vowsound Electronics Co., Ltd. , https://www.vowsound.com